NEWS
Happy Holidays
The end of 2018 is here already! X41 wishes you a lot of fun in the next few weeks and hopes all of you are able to get some time off.
2018 was exciting for X41 and everyone involved. We are proud that our contributions to research were accepted by several conferences, and that public audits were released by some of our customers. X41 is growing and our team has got bigger, with new, highly skilled members on board!
2018 began with a talk by Markus at Offensive Con about the dangers of WebUSB. He and Michele Orrù presented attacks against FIDO U2F and showed a demo against YubiKey. The research attracted a lot of attention and was featured in several articles, including one from Wired.
In March, Eric traveled to the beautiful beaches of Goa to present some insights into different IoT Operating Systems (Contiki, Apache MyNewt, RIOT, Zephyr) at Nullcon. Furthermore, other results of Kudelski and our audit of the Wire mobile phone and web clients were released.

In July, Niklas went to Lille to present his research on shadowsocks at Pass The Salt in Lille. He identified several flaws in implementation and design that could impact users of shadowsocks in significant ways.

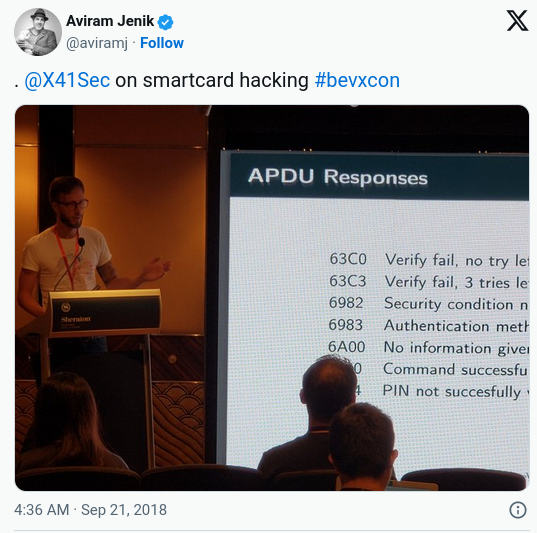
Eric went to Las Vegas in August, to attend defcon 26, where he demonstrated some attacks on smartcard drivers and released several fuzzing tools that aid in finding further bugs. He went into a bit more detail in October at beVX in Hong Kong.
In the same month, we were happy that Mozilla decided to publish the results of our review of the updater for Mozilla Firefox. It is available here.
One of the most interesting research projects we had in 2018 was hacking faxes! X41 started this research early in 2018, and discovered several flaws in enterprise-class fax servers and fax clients. The vulnerabilities even allowed remote compromise-and-command execution using only the phone line! We released advisories on bugs in Linux fax software, and Luis did a great writeup on the topic. Unfortunately, he could not join Markus and Eric in Saint Petersburg at zeronights in November to present the topic. Nevertheless, our slides were made available.
In 2019, X41 will have more exciting contributions to make, so stay tuned! Happy Holidays!
About X41 D-Sec GmbH
X41 D-Sec GmbH is an expert provider of application security services. Having extensive industry experience and expertise in information security enables X41’s strong core team of world-class experts to perform premium security services.
Fields of expertise in application security are security-centric code reviews, binary reverse engineering, and vulnerability discovery. Custom research and IT-security consulting and support services are core competencies of X41.